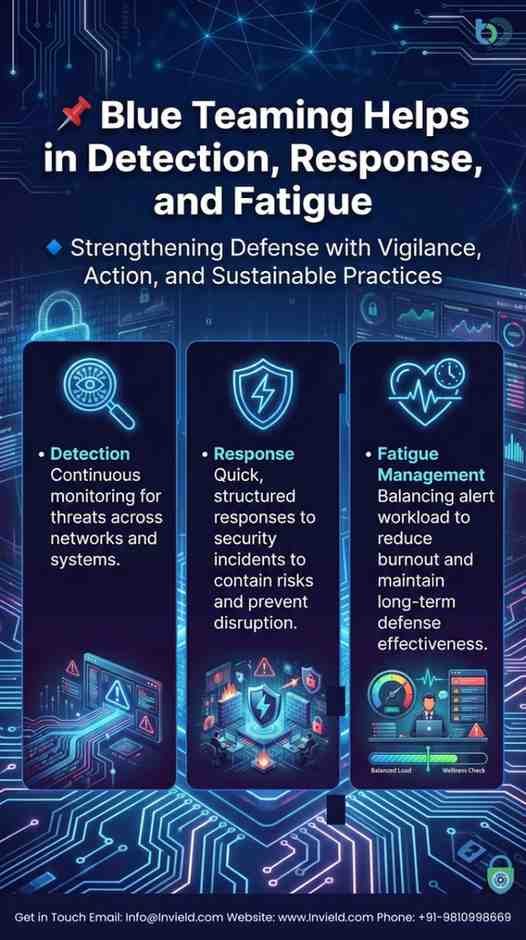
Blue Teaming Helps in Detection, Response, and Fatigue
today’s rapidly evolving digital landscape, cyber threats continue to grow in volume, sophistication, and impact. Organizations face a constant barrage of malicious attacks from ransomware and phishing to advanced persistent threats (APTs) making robust cyber defense more vital than ever. At the heart of a strong cybersecurity posture lies Blue Teaming, a strategic defensive approach central to effective cyber threat detection, incident response, and managing alert fatigue within security teams.
Blue Teaming refers to the set of defensive cybersecurity practices carried out by security professionals whose mission is to protect an organization’s networks, systems, and data from cyberattacks. These professionals, often integrated within a Security Operations Centre (SOC), are responsible for continuous monitoring, analysing, and defending against threats—a function that is both proactive and reactive.
The Role of Blue Teams in Cyber Threat Detection
One of the foundational pillars of Blue Teaming is cyber threat detection. Detection is the ability to recognize indicators of compromise (IOCs) and suspicious activity in real time before they evolve into a full-blown security incident. Blue Teams use an ecosystem of defensive tools and advanced monitoring methods to accomplish this.
A primary detection tool in Blue Team operations is the Security Information and Event Management (SIEM) platform. SIEM systems aggregate and correlate security log data from across networks, endpoints, and applications, allowing analysts to spot anomalies, suspicious patterns, and early warning signs of cyberattacks. When continuous monitoring is combined with Endpoint Detection and Response (EDR) tools and network sensors, defenders gain deep visibility into potential threat vectors.
In addition to tool-based methods, Blue Teaming also employs threat hunting—a proactive technique where security analysts search for hidden threats that evade automated detection. Threat hunting improves detection accuracy and reduces blind spots by uncovering subtle signs of compromise that might otherwise be missed.
Continuous detection isn’t just reactive; it also empowers organizations to adapt their defences over time. By analysing attack patterns, threat intelligence feeds, and telemetry data, Blue Teams can refine SIEM rules, optimize alert thresholds, and tune behavior-based detection to catch sophisticated threats faster.
Incident Response: Swift and Structured Action
Detection alone is not enough—once a threat is identified, incident response becomes crucial. Blue Teams play a leading role in structuring and executing incident response procedures to contain, eradicate, and remediate cyber threats quickly and efficiently.
Incident response typically follows a well-defined process:
- Identification: Confirming the presence of a security event.
- Containment: Limiting the spread of the threat.
- Eradication: Eliminating the root cause of the incident.
- Recovery: Restoring normal operations.
- Lessons Learned: Reviewing the incident to improve defences.
Effective incident response depends on preparation and coordination. Blue Teams develop and maintain Incident Response Plans (IRPs) that outline roles, responsibilities, communication workflows, and technical playbooks. These plans ensure that response actions are timely, efficient, and aligned with organizational priorities, minimizing potential disruption.
Blue Teams also perform post-incident forensics, which involves analysing attack artifacts, reconstructing the attacker’s path, and identifying exploited vulnerabilities. This intelligence feeds back into detection and prevention strategies, creating a cycle of continuous improvement.
Addressing SOC Alert Fatigue
As threat detection technologies become more advanced, they also generate increasing volumes of alerts. Too many alerts—especially false positives—can overwhelm security analysts, leading to SOC alert fatigue. When analysts are inundated with repetitive, low-priority alerts, their ability to focus on true threats diminishes, increasing the risk of missed detections.
Alert fatigue is one of the biggest challenges Blue Teams faces. It reduces team effectiveness, accelerates burnout, and undermines long-term operational sustainability. Managing alert fatigue requires a multi-pronged approach:
- Detection Engineering: Blue Teams continuously refine and tune detection rules to reduce false positives and improve signal quality. Effective tuning ensures that only relevant and high-impact alerts escalate to human analysts.
- Automated Triage and Prioritization: Leveraging machine learning and automation capabilities within SIEM and SOAR (Security Orchestration, Automation, and Response) systems helps automate the initial classification of alerts. Automating triage allows analysts to focus on high-severity incidents instead of routine noise.
- Prioritization Frameworks: Blue Teams implement prioritization models that rank alerts based on severity, asset importance, and potential impact, ensuring critical threats receive immediate attention.
By optimizing alert workflows and integrating automation, Blue Teams not only reduce alert fatigue but also increase overall responsiveness and boost morale among cybersecurity analysts.
Collaborative Defense and Purple Teaming
While Blue Teaming focuses on defense, many organizations adopt Purple Teaming—a collaborative model where Blue and Red Teams work together. Instead of operating in isolation, offensive (Red Team) and defensive (Blue Team) professionals share insights and simulate real-world attack scenarios in a controlled environment. This collaboration accelerates detection refinement and strengthens incident response strategies.
Purple Team exercises help Blue Teams understand attacker behavior patterns, improve detection rules, and fine-tune incident response playbooks based on simulated threat activity. This practical feedback loop enhances overall security posture more rapidly than traditional siloed operations.
AI, Automation, and Blue Teaming Evolution
The future of Blue Teaming lies in intelligent automation and artificial intelligence (AI). Emerging solutions aim to augment human defenders with AI-driven analysis, automated threat prioritization, and adaptive response orchestration. These advancements not only increase detection and response speed but also play a significant role in combating alert fatigue.
By combining AI with structured Blue Team techniques and human expertise, organizations can evolve their defensive capabilities to meet the challenges of complex and fast-moving cyber threats.
Blue Teaming is a critical component of modern cybersecurity, enabling organizations to improve their cyber threat detection, accelerate incident response, and mitigate alert fatigue among defense teams. Through a combination of advanced tools, structured playbooks, continuous monitoring, and collaborative frameworks like Purple Teaming, Blue Teams ensure that defences stay resilient in the face of evolving threats. As cyber risks grow in complexity, investing in robust Blue Team operations is not just advantageous—it’s essential for long-term cyber resilience.
Comments
Post a Comment