Integrating Dark Web Monitoring with Incident Response
Integrating Dark Web Monitoring with Incident Response reveals a critical shift in how organizations handle modern threats. Over the years of working closely with organizations across industries, one pattern has consistently stood out. The earliest signs of trouble rarely originate within systems. They surface quietly; in places most teams don’t actively watch the dark web.
What makes the difference isn’t just spotting those signals. It’s what happens in the moments after they are discovered. That’s where security either holds or begins to slip.
Why Integrating Dark Web Monitoring with Incident Response Is Essential
There’s a familiar story many security teams recognize. An incident has been discovered. Systems are checked. Access logs are reviewed. And somewhere along the way, someone uncovers a frustrating detail; sensitive information had already been exposed days or even weeks earlier on the dark web. That moment often raises the same question: Could this have been prevented? Dark web monitoring exists to answer that question with a “yes.” It gives organizations a chance to see trouble forming before it hits internal systems.
It helps surface:
- Leaked employee credentials before attackers start using them
- Sensitive company data circulating in underground spaces
- Early chatter that hints at planned attacks
- Exposure through vendors or partners that might otherwise go unnoticed
But here’s the catch, just knowing this isn’t enough.
Where Integrating Dark Web Monitoring with Incident Response Falls Short
In many environments, the gap isn’t about a lack of tools or intelligence. It’s about what happens after the alert arrives. An exposed credential might be flagged, but the response is delayed. A report might be reviewed later in the day, or even the next. Meanwhile, the threat continues to evolve in real time. Attackers don’t wait for internal workflows to catch up. This delay sometimes just a few hours is often enough to turn a manageable risk into a serious incident.
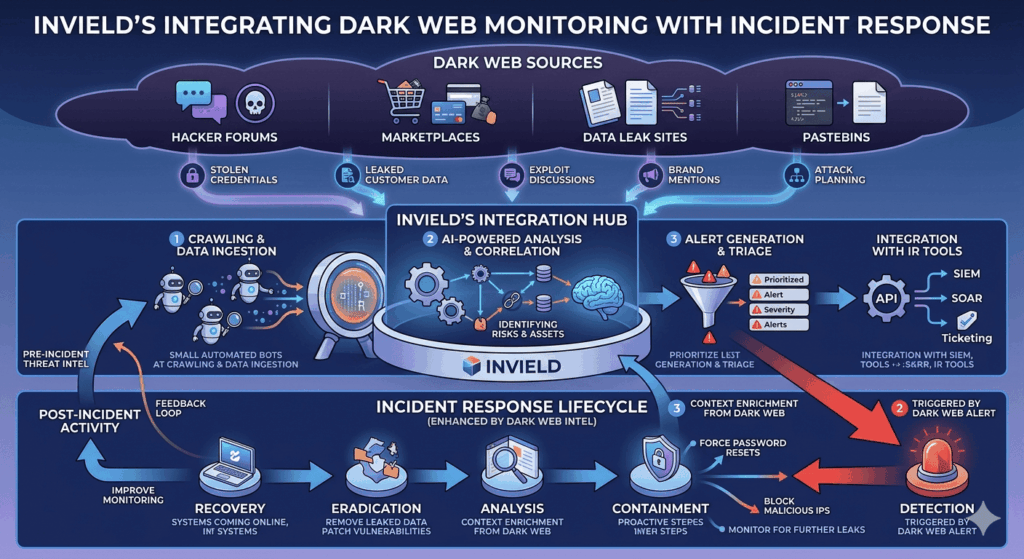
How Invield Enables Integrating Dark Web Monitoring with Incident Response
Integration, as approached at Invield, isn’t about layering more complexity onto an already crowded security stack. It’s about creating a clear and immediate path from signal to response. The focus is on ensuring that every meaningful piece of intelligence leads to a defined action without hesitation, and without unnecessary friction.
1. Turning Raw Signals into Clear Priorities
Not every piece of data deserves urgency, and that’s where many teams struggle. The dark web is noisy, and without context, it’s easy to either overreact or overlook something important. The approach begins by quickly understanding what truly matters. When a credential appears, the first step is to determine whether it’s still relevant, whether it belongs to a high-risk account, and whether there’s any indication it’s being actively used. That layer of clarity makes all the difference. It ensures that attention is directed toward real threats rather than distractions.
2. Responding Without Delay
Speed has a way of shaping outcomes in cybersecurity. But speed without direction can create its own problems, so the emphasis is acting quickly with purpose.
At Invield, response actions are not improvised at the moment. They are anticipated and built into the process. When a credible threat is identified, the response begins immediately, whether that means securing accounts, tightening access controls, or increasing monitoring. This removes hesitation from the equation. It allows teams to move with confidence rather than pause for debate.
3. Embedding Intelligence into Incident Workflows
One of the most practical shifts comes from making dark web intelligence part of everyday incident response, not something that sits outside of it. When this integration is done well, there’s no confusion about the next steps. Teams don’t need to stop and figure out who should act or how. The process is already in place, and the response flows naturally from the alert. It creates a sense of structure in moments that would otherwise feel uncertain. And in high-pressure situations, that structure becomes incredibly valuable.
4. Learning and Adapting Continuously
Every incident, no matter how small, carries insight. Over time, patterns begin to emerge—certain signals prove more reliable; certain responses prove more effective, and certain gaps become easier to spot.
At Invield, these moments are treated as opportunities to refine the system. The goal isn’t just to respond well today, but to respond even better tomorrow. That continuous adjustment is what gradually strengthens the entire security posture.
Real-World Impact of Integrating Dark Web Monitoring with Incident Response
A financial services organization once experienced a series of unusual login attempts. Nothing is immediately critical but persistent enough to raise concern. Traditional tools didn’t offer a clear explanation. Then came a key insight: a small set of employee credentials had appeared on a dark web forum. At that moment, the difference wasn’t in the discovery; it was in response.
Instead of treating it as background intelligence, the organization acted immediately:
- Credentials were invalidated
- Users were guided through secure resets
- Access logs were reviewed alongside the exposure
- Additional monitoring was activated
Within a short span, the suspicious activity stopped. The threat didn’t escalate because it was addressed early. That’s the impact of integration done right.
Challenges in Integrating Dark Web Monitoring with Incident Response
Of course, this approach doesn’t come without its difficulties. The sheer volume of data from dark web sources can feel overwhelming without proper filtering. Not every signal is accurate, which introduces the risk of false alarms. In some organizations, teams still operate in silos, which slows coordination at critical moments. There’s also the practical challenge of resources building automation, refining workflows, and maintaining alignment takes effort. But these challenges aren’t barriers. They’re indicators of where systems need to evolve. With the right focus, each one can be addressed in a way that strengthens the overall approach.
What Effective Integrating Dark Web Monitoring with Incident Response Looks Like
When dark web monitoring and incident response are fully aligned, the shift is noticeable. There’s less uncertainty. Fewer delays. More control. It often looks like:
- Early warnings triggering immediate, confident action
- Teams working from shared, well-defined processes
- Reduced time between detection and response
- Continuous refinement based on real-world experience
It doesn’t feel reactive. It feels prepared.
Why This Matters More Than Ever
Threats today don’t appear suddenly; they develop over time, often leaving traces well before they reach internal systems. Organizations that rely solely on internal detection often react too late. By integrating dark web monitoring with incident response, that dynamic begins to shift. External visibility becomes an advantage rather than an afterthought.
It leads to faster containment, reduced exposure, and a deeper understanding of how threats evolve outside the organization’s immediate view. More importantly, it builds confidence because responses are no longer delayed or uncertain.
Conclusion: The Future of Integrating Dark Web Monitoring with Incident Response
Invield’s experience continues to reinforce a simple truth: the value of intelligence lies in how it’s used. Dark web monitoring provides a rare opportunity to see risks forming early. But that opportunity only becomes meaningful when it’s connected to a system that knows how to respond and does so without hesitation.
Because in the end, security isn’t defined by how much is known. It’s defined by how effective action follows. And those who act early are the ones who stay ahead.
Comments
Post a Comment